- Introduction
- Architectural Evolution: The Path to SSP 5.1
- The vDefend 1-2-3-4 Security Journey
- The VCF 9.0.X Project-Level Security Checklist
- Intelligent Assist (GenAI) for SecOps
- Conclusion
Introduction
The transition to VMware Cloud Foundation (VCF) 9.0.x marks an evolution from disparate software-defined components to a unified private cloud platform. While the architectural shift toward the Security Services Platform (SSP) began in the NSX 4.2 cycle,(VCF 5.2), VCF 9.0 is the first release to fully operationalize this engine as the heart of a unified security model.
By leveraging SSP 5.1, VCF 9.0.X automates the transition from raw network traffic discovery to enforced Zero Trust policies through a new, centralized vDefend 1-2-3-4 journey.
Architectural Evolution: The Path to SSP 5.1
The transition from the legacy NSX Application Platform (NAPP) to the streamlined SSP is a multi-release evolution. While SSP support was introduced for NSX 4.2.x (paired with VCF 5.2), VCF 9.0 makes this architecture the native standard for fleet-level security operations.
| Feature | VCF 5.2 / NSX 4.2.x (Transition) | VCF 9.0 (Unified Platform) |
| Security Engine | Support for SSP 5.0/5.1 begins. | SSP 5.1 is the native standard for the fleet. |
| Workflow Interface | Fragmented per-service configuration. | Unified “vDefend 1-2-3-4” journey console. |
| Management Scope | Siloed management via individual managers. | VCF Operations Console fleet-wide view. |
| Automation Level | Manual triggers for discovery. | Autonomous drift detection and alert cycles. |
The vDefend 1-2-3-4 Security Journey
VCF 9.0 formalizes security operations through a prescriptive four-stage journey hosted on the SSP. Below is the technical breakdown of the key phases.
Phase 1: Discovery & Assessment (SSP Stage 1)
In this initial stage, the Security Intelligence engine ingests vFix (IPFIX) metadata directly from the ESXi kernel to baseline “East-West” traffic.
Heuristic Clustering: The AI clusters VMs (AI logicalizes VMs)into logical “Application Workspaces” based on communication frequency .
Security Posture Scoring: The system generates a “Security Segmentation Score” to quantify current exposure and identify unprotected flows.
Capture 1: –
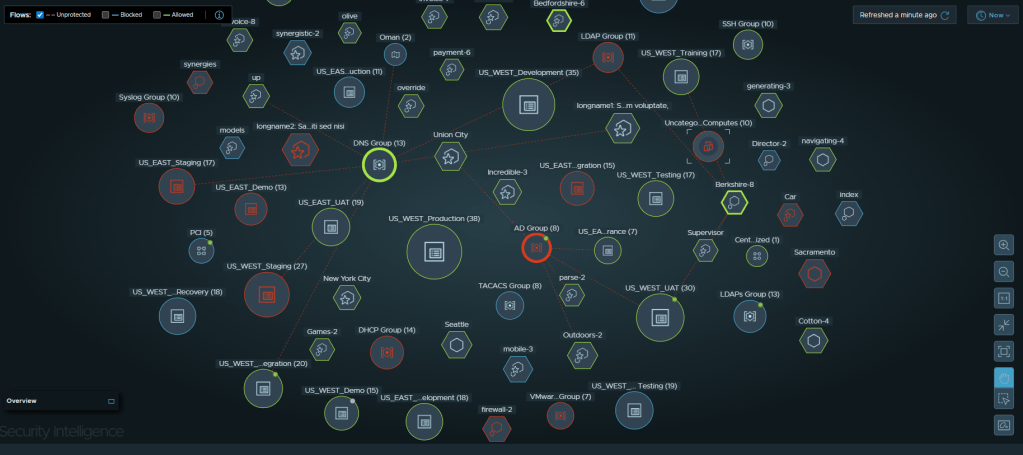
As per capture 1 : -AI-driven discovery in VCF 9.0.X. Red dashed lines represent flows identified by the engine as “Unprotected,” mapping the gap between current state and Zero Trust.
Phase 2: Infrastructure Protection (SSP Stage 2)
This phase focuses on securing core backbone services such as DNS, DHCP, NTP, and LDAP.
Automated Discovery: The SSP 5.1 engine scans the environment to identify these critical infrastructure assets.
Service-Based Policies: Instead of static IP lists, the system proposes policies based on the specific role of the infrastructure service.
Capture 2: –
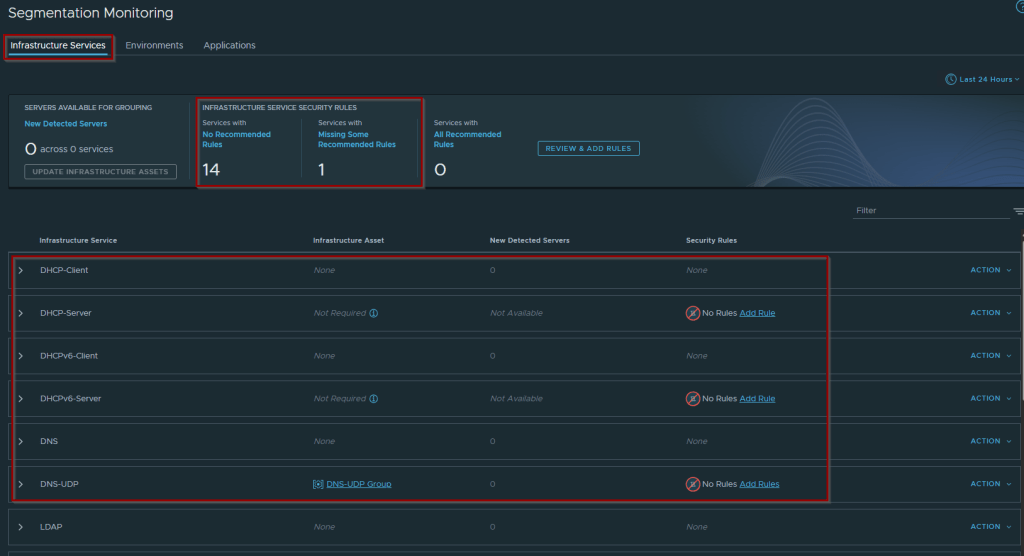
As per Capture 2:- Infrastructure Service Monitoring. This dashboard identifies discovered core services and highlights those lacking recommended security rules.
Phase 3: Environment-Level Protection (SSP Stage 3)
Phase 3 establishes macro-level security boundaries between major security zones, such as Development, QA, and Production.
- Zone Segmentation: Strict boundaries are established to reduce the overall attack surface and limit the “blast radius” of a potential compromise.
- Leakage Monitoring: The system continuously monitors for traffic “leakage” between zones and alerts users to unauthorized inter-zone communication.
- Metadata-Driven Grouping: Administrators can import VM-to-zone mappings via CSV to automatically categorize assets and apply security tags.
Phase 4: Application-Level Micro-segmentation (SSP Stage 4)
The final stage leverages the full power of Security Intelligence to create granular “Application Ring-fencing”.
- Policy Synthesis: The AI processes historical flow data to recommend specific Distributed Firewall (DFW) rules.
- Continuous Monitoring: The system detects changes in the environment (drift) and prompts for rule updates to maintain the integrity of the security boundary.
Capture 3: –
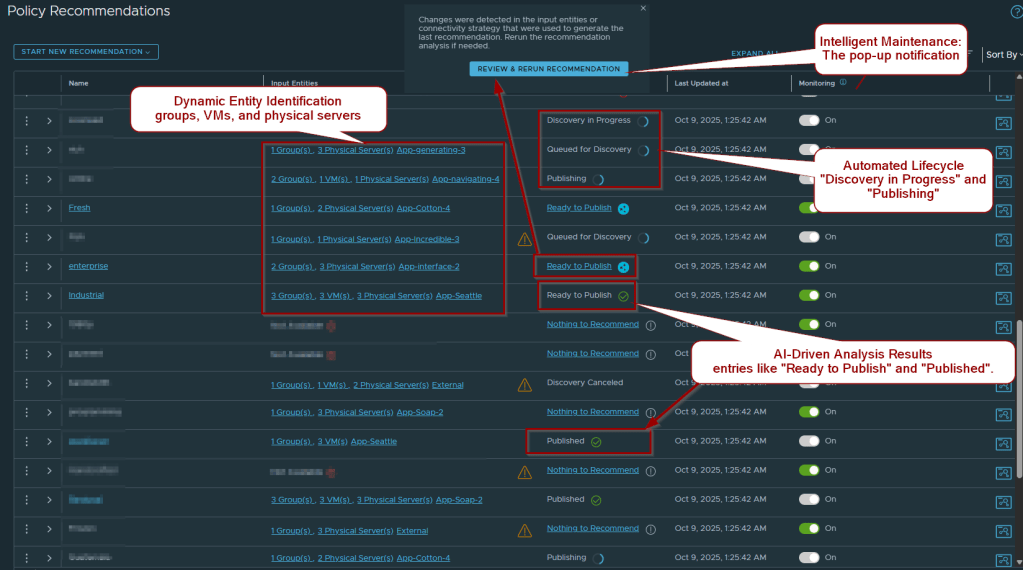
As per capture 3: -AI Policy Recommendations. The engine proposes granular rules for complex applications (e.g., payment, workforce) with a “Ready to Publish” status.
The VCF 9.0.X Project-Level Security Checklist
In VCF 9.0.X, security is no longer a “one-size-fits-all” global configuration. With the introduction of NSX Projects and VPCs, security is now delegated. Use this checklist to ensure your environment is ready for AI-driven automation.
| Category | Action Item | Architectural Goal |
| Governance | Define Project Guardrails | Enforce non-overrideable ‘Top-Tier’ security policies across VPCs. |
| Platform | Activate SSP 5.1 | Deploy Security Services Platform in workload domains to replace legacy NAPP. |
| RBAC | Assign VPC Admin Roles | Delegate security approvals to app owners within their isolated logical space. |
| Visibility | Enable Security Intelligence | Activate flow analysis for specific clusters hosting critical workloads. |
| Automation | Standardize Tagging Metadata | Prepare CSV environment mappings for Stage 3 bulk-categorization. |
| Analysis | Set Discovery Intervals | Allow 24-48 hours of traffic baselining before rule generation. |
| Operations | Initialize Intelligent Assist | Configure GenAI for natural language threat triage and remediation. |
Intelligent Assist (GenAI) for SecOps
- VCF 9.0.X introduces Intelligent Assist, a Large Language Model (LLM) interface that acts as a security co-pilot.
- Natural Language Queries: Admins can query the platform (for e.g., “Explain the threat campaign targeting the production VPC“).
- Delegated Enforcement via VPCs: VCF 9.0.X introduces VPC-Aware Lateral Security. Infrastructure teams set global “Guardrails,” but the AI allows VPC Admins (Application Owners) to auto-generate and manage rules for their own apps within their isolated space. This removes the “Security Bottleneck.”
- Automated Remediation: The AI provides context for security events and offers one-click buttons to auto-generate emergency block rules or quarantine compromised workloads.
Conclusion
By leveraging SSP 5.1, VCF 9.0.X transforms security into a proactive discipline. While SSP support began in the VCF 5.2 era, VCF 9.0.X is where this architecture is unified into a prescriptive journey. This staged approach ensures organizations can systematically reduce their attack surface while maintaining operational agility.. In this new architecture, AI does the heavy lifting of traffic analysis, allowing architects to focus on high-level security intent rather than manual rule maintenance.
************************************************************
LinkedIn Promotion Kit
Headline: Zero Trust is now Autonomous in VCF 9.0.X 🚀
Stop fighting with manual firewall spreadsheets. VMware Cloud Foundation (VCF) 9.0.X has officially operationalized AI-driven security through the Security Services Platform (SSP) 5.1.
In my latest blog, I break down the vDefend 1-2-3-4 Journey:
🔹 Phase 1: Discovery – AI-baselining of all East-West traffic.
🔹 Phase 2: Infrastructure – Auto-securing DNS, DHCP, and Active Directory.
🔹 Phase 3: Environments – Bulk-tagging zones (Prod/Dev) via CSV metadata.
🔹 Phase 4: Applications – AI-synthesized micro-segmentation rules.
I also dive into Intelligent Assist, the GenAI co-pilot that lets you triage threats using plain English.
Whether you’re on VCF 5.2 or moving to 9.0, the shift from legacy NAPP to the streamlined SSP engine is the architectural foundation you need to know.
🔗 Read the full technical deep dive: [Insert Your Blog Link]
*************************************************************************


Leave a comment